This datasheet showcases how Surface devices can address the unique challenges faced by various roles in manufacturing.
Supporting Devices Needs for Manufacturers
This eBrochure provides information on how Microsoft Surface for Business can empower manufacturers’ workforce with versatile devices, boosting productivity and ensuring security.
The future of business is here: How industries are unlocking AI innovation and greater value with the Microsoft Cloud
IT departments are facing a growing application backlog because of the lack of developers and technical specialists who can produce these solutions. Read this urgent blog about an answer to this problem: low code. This is the solution that empowers IT departments to rapidly build apps and streamline data insights while lowering costs.
HEINEKEN connects employees with information across the company using Azure AI Services
Many forward-thinking corporations are using technology to build connections between its management and the information they need to make impactful, data-driven decisions. Read this insightful customer story about how Heineken uses Azure OpenAI to bring innovation to its business processes.
Meet the New Surface Laptop Studio 2
This video showcases the laptop’s cutting-edge features and exceptional benefits, including its sleek design, powerful performance, and versatile functionality.
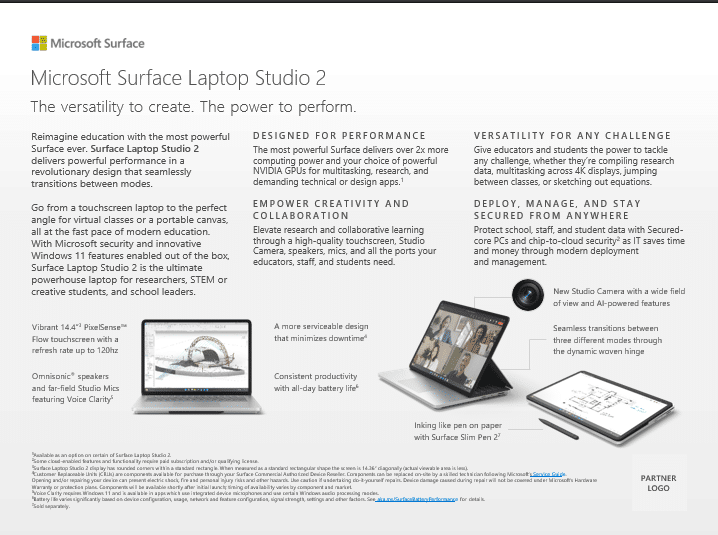
Microsoft Surface Laptop Studio 2 Flyer
This solution brief answers questions about the purpose and design, performance and features, hardware specifications, and connectivity and software.
Azure OpenAI Service: 10 ways generative AI is transforming businesses
Generative AI is proving to be an essential tool in many industries, creating realistic images and videos that enhance the customer experience. Read this enlightening blog about the ten ways generative AI is being used by organizations to transform their operations and drive growth.
How AI Enhances Endpoint Detection and Response (EDR) for Stronger Cybersecurity
Bill Doerrfeld explains how AI is improving endpoint threat detection and accelerating response times.
Book a free demo of a powerful AI cybersecurity solution
If you’re finding it increasingly difficult and time consuming to defend against today’s cyberthreats, we have a cost-effective AI-powered cybersecurity solution that can significantly enhance your defenses. Book your free demo today.
View: Book a free demo of a powerful AI cybersecurity solution
How Generative AI Will Remake Cybersecurity
IT and cybersecurity vendors are rolling out generative AI security tools. Learn more about LLM security tools and trends.